Your cart is currently empty!

Feb 27, 2025Ravie LakshmananCybercrime / Android Cybersecurity researchers have discovered an updated version of an Android malware called TgToxic (aka ToxicPanda), indicating that the threat actors behind it are continuously making changes in response to public reporting. “The modifications seen in the TgToxic payloads reflect the actors’ ongoing surveillance of open source intelligence and demonstrate…

Feb 27, 2025The Hacker NewsArtificial Intelligence / Browser Security Organizations are either already adopting GenAI solutions, evaluating strategies for integrating these tools into their business plans, or both. To drive informed decision-making and effective planning, the availability of hard data is essential—yet such data remains surprisingly scarce. The “Enterprise GenAI Data Security Report 2025” by…
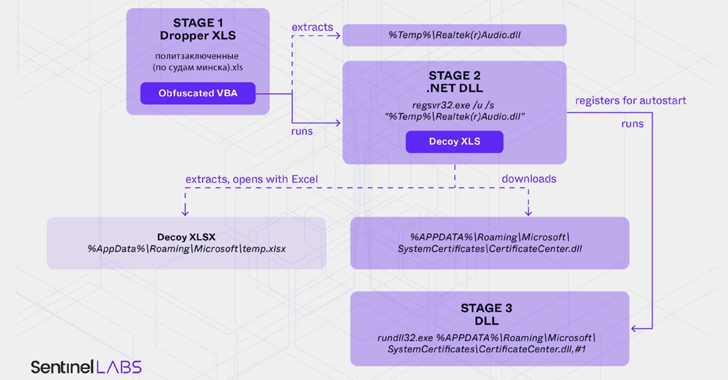
Feb 25, 2025Ravie LakshmananMalware / Cyber Espionage Opposition activists in Belarus as well as Ukrainian military and government organizations are the target of a new campaign that employs malware-laced Microsoft Excel documents as lures to deliver a new variant of PicassoLoader. The threat cluster has been assessed to be an extension of a long-running campaign…

Cybersecurity researchers have flagged an updated version of the LightSpy implant that comes equipped with an expanded set of data collection features to extract information from social media platforms like Facebook and Instagram. LightSpy is the name given to a modular spyware that’s capable of infecting both Windows and Apple systems with an aim to…
Feb 26, 2025Ravie LakshmananEnterprise Security / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday placed two security flaws impacting Microsoft Partner Center and Synacor Zimbra Collaboration Suite (ZCS) to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerabilities in question are as follows – CVE-2024-49035 (CVSS score:…

Feb 26, 2025Ravie LakshmananMalware / Cryptocurrency Cybersecurity researchers have flagged a malicious Python library on the Python Package Index (PyPI) repository that facilitates unauthorized music downloads from music streaming service Deezer. The package in question is automslc, which has been downloaded over 104,000 times to date. First published in May 2019, it remains available on…

Feb 26, 2025Ravie LakshmananNetwork Security / Threat Intelligence The Computer Emergency Response Team of Ukraine (CERT-UA) on Tuesday warned of renewed activity from an organized criminal group it tracks as UAC-0173 that involves infecting computers with a remote access trojan named DCRat (aka DarkCrystal RAT). The Ukrainian cybersecurity authority said it observed the latest attack…

Feb 26, 2025The Hacker NewsIdentity Protection / Password Security Passwords are rarely appreciated until a security breach occurs; suffice to say, the importance of a strong password becomes clear only when faced with the consequences of a weak one. However, most end users are unaware of just how vulnerable their passwords are to the most…

Mar 07, 2025Ravie LakshmananCryptocurrency / Ransomware A coalition of international law enforcement agencies has seized the website associated with the cryptocurrency exchange Garantex (“garantex[.]org”), nearly three years after the service was sanctioned by the U.S. Treasury Department in April 2022. “The domain for Garantex has been seized by the United States Secret Service pursuant to…

Mar 07, 2025Ravie LakshmananMalware / Blockchain Cybersecurity researchers have discovered a malicious Python package on the Python Package Index (PyPI) repository that’s equipped to steal a victim’s Ethereum private keys by impersonating popular libraries. The package in question is set-utils, which has received 1,077 downloads to date. It’s no longer available for download from the…
